The WatchGuard L2TP Setup Wizard helps you activate and configure Mobile VPN with L2TP on the Firebox. The setup wizard is available only when Mobile VPN with L2TP is not activated. The wizard prompts you to configure these settings:
- Authentication server
- Users and groups
- Virtual IP address pool
- Authentication method
Settings not included in the wizard are set to their default values. After you complete the wizard, you can edit the Mobile VPN with L2TP configuration to change settings you specified in the wizard and other settings.
You cannot configure Mobile VPN with L2TP if the device configuration already has a branch office VPN gateway that uses main mode and has a remote gateway with a dynamic IP address.
Before You Begin
Authentication Server
You must configure an authentication server for L2TP user authentication before you enable Mobile VPN with L2TP. Make sure that any users and groups you want to use are added to the authentication server. When you configure Mobile VPN with L2TP, you select an authentication server and specify users and groups.
Mobile VPN with L2TP supports two authentication methods: Local authentication on the Firebox (Firebox-DB) and RADIUS. For more information about supported user authentication methods for L2TP, go to About Mobile VPN with L2TP User Authentication.
Dynamic IP Address
If your Firebox has a dynamic IP address, you can configure dynamic DNS so users can specify a domain name in the client settings to connect to the VPN. Make sure to register the external IP address of your Firebox with a dynamic DNS service provider. Optionally, you can enable dynamic DNS on the Firebox to automatically send IP address updates to a dynamic DNS service provider that the Firebox supports. For more information about dynamic DNS, go to About the Dynamic DNS Service.
Network Access Enforcement
To limit mobile VPN connections to devices that follow corporate policy, you can use network access enforcement. Before you enable network access enforcement for groups specified in the Mobile VPN with LT2P configuration, enable and configure network access enforcement at Subscription Services > Network Access Enforcement (Fireware v12.9 or higher). For more information, go to Network Access Enforcement Overview.
In Fireware v12.5.4 to v12.8.x, this feature was called TDR Host Sensor Enforcement. TDR is now end of life and cannot be used for network access enforcement. In the user interface, this feature is no longer functional but is required by the configuration schema. To enable network access enforcement, we recommend that you upgrade to EDR Core. For more information, go to this Knowledge Base article: Host Sensor Upgrade to Endpoint Security.
Default Settings
IPSec
When you activate Mobile VPN with L2TP, IPSec is enabled by default with these IPSec settings:
Phase 1 transforms:
- SHA-1, AES(256), and Diffie-Hellman Group 2
- SHA-1, AES(256), and Diffie-Hellman Group 20
- SHA2-256, AES(256), and Diffie-Hellman Group 14
The SA life is 8 hours for all transforms.
Phase 2 proposals:
- ESP-AES-SHA1
- ESP-AES128-SHA1
- ESP-AES256-SHA256
PFS is disabled by default.
IP Address Pool
By default, the Mobile VPN with L2TP address pool is 192.168.115.0/24.
We recommend that you do not use the private network ranges 192.168.0.0/24 or 192.168.1.0/24 on your corporate or guest networks. These ranges are commonly used on home networks. If a mobile VPN user has a home network range that overlaps with your corporate network range, traffic from the user does not go through the VPN tunnel. To resolve this issue, we recommend that you Migrate to a New Local Network Range.
For more information about virtual IP address pools, go to Virtual IP Addresses and Mobile VPNs.
User Group
When you enable Mobile VPN with L2TP, the Firebox automatically creates a user group named L2TP-Users. You can add other users and groups in the L2TP configuration. The Firebox automatically includes those users and groups in the L2TP-Users group.
For information about user authentication and multi-factor authentication, go to About Mobile VPN with L2TP User Authentication.
Policy
When you activate Mobile VPN with L2TP, the Firebox automatically creates three policies: Allow-IKE-to-Firebox, which is a hidden IPSec policy, Allow L2TP-Users, and WatchGuard L2TP.
The Allow L2TP-Users policy allows the groups and users you configured for L2TP authentication to get access to resources on your network. By default, the To list in the policy includes only the alias Any, which means this policy allows Mobile VPN with L2TP users to access to all network resources.
We recommend that you limit which network resources that Mobile VPN with L2TP users can access through the VPN. To do this, you can replace the Allow L2TP-Users policy. For instructions that explain how to replace the Allow L2TP-Users policy, and for more information about L2TP policies, go to About L2TP Policies.
Other Settings
After you complete the wizard, you can configure additional Mobile VPN with L2TP settings that do not appear in the wizard. For information about other settings, go to Edit the Mobile VPN with L2TP Configuration.
Use the L2TP Setup Wizard
The steps to start the wizard changed in Fireware v12.3. To start the wizard in Fireware Web UI v12.2.1 or lower, select VPN > Mobile VPN with L2TP and click Run Wizard. To start the wizard in Policy Manager v12.2.1 or lower, select VPN > Mobile VPN > L2TP > Activate.
- Select VPN > Mobile VPN.
- In the L2TP section, click Launch Wizard.
The Mobile VPN with L2TP wizard opens. - Click Next.
A list of authentication servers opens.
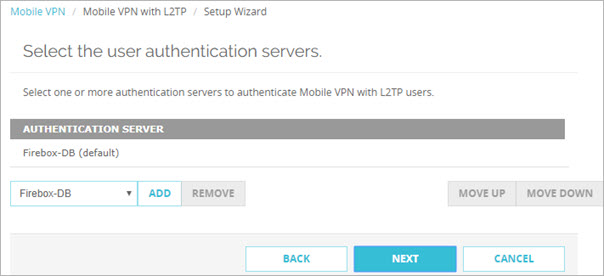
- From the Authentication Server list, select a server.
- Click Add. You can add the internal Firebox database (Firebox-DB) and one or more RADIUS servers.
For more information about user authentication methods for L2TP, go to About Mobile VPN with L2TP User Authentication. - To specify a different default server, select that server and click Move Up. The server that appears first in the list is the default server.
If users do not specify the authentication server as part of the user name when they authentication from an L2TP client, Mobile VPN with L2TP uses the default authentication server.
If you select more than one authentication server, users who use the non-default authentication server must specify the authentication server or domain as part of the user name. For more information and examples, go to Connect from an L2TP VPN Client.
- Click Next.
The Authentication Users and Groups page opens. The L2TP-Users group is automatically added by default.
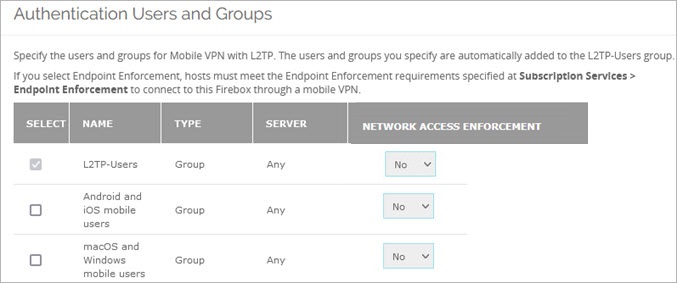
- Select the users or groups for Mobile VPN with L2TP.
- (Optional) To apply enforcement settings to Mobile VPN with L2TP groups:
- Select the check box for a group.
- In Fireware v12.9 or higher, in the Network Access Enforcement column, select Yes.
- To disable enforcement for a group, select the check box for that group and select No.
- To add new users or groups to authenticate with Mobile VPN with L2TP:
- In the Create new section, from the first drop-down list, select Any, Firebox-DB, or RADIUS.
- From the adjacent drop-down list, select User or Group.
- Click Add.
- If you selected Any or RADIUS for the authentication server, configure the settings in the Add User or Group dialog box.
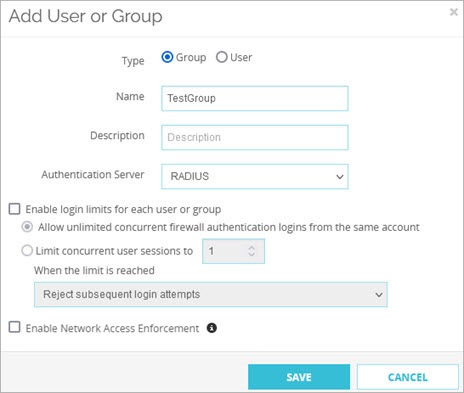
- If you selected Firebox-DB for the authentication server, configure the settings in the Firebox User or Firebox Group dialog box.
- (Optional) To apply enforcement settings to the group in Fireware v12.9 or higher, select Enable Network Access Enforcement. For more information, go to Network Access Enforcement Overview.
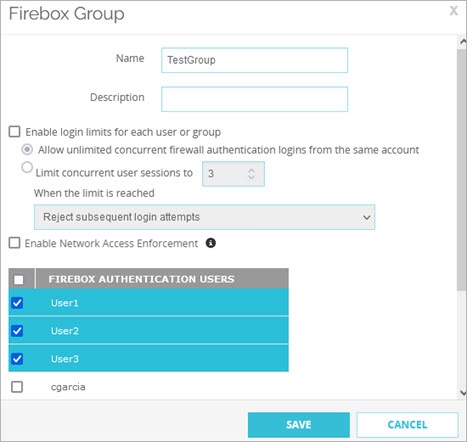
If you use Firebox-DB for authentication you must use the L2TP-Users group that is created by default. You can add the names of other groups and users that use Mobile VPN with L2TP. For each group or user you add, you can select the authentication server where the group exists, or select Any if that group exists on more than one authentication server. The group or user name you add must exist on the authentication server. The group and user names are case sensitive and must exactly match the name on your authentication server.
- After you configure users and groups, click Next.
The Virtual IP Address Pool page opens. By default, the 192.168.115.0/24 network shows in the list.
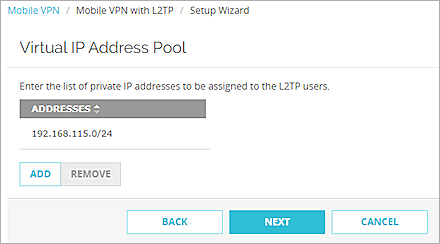
- To add a new IP address pool, click Add.
The Add Address Pool dialog box opens.
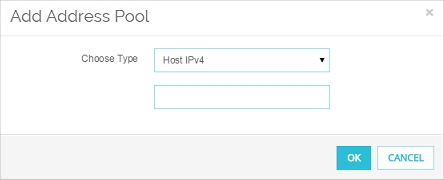
- In the Choose Type drop-down list, select whether to add an IPv4 host address, network address, or address range. You must add at least two IP addresses to the virtual IP address pool. Type the IP address or range and click OK.
The address is added to the virtual IP address pool.
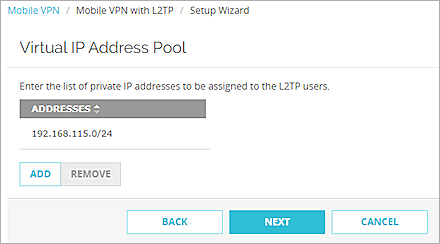
For more information about virtual IP address pools, go to Virtual IP Addresses and Mobile VPNs.
- After you define the virtual IP address pool, click Next.
The Tunnel authentication method page opens.
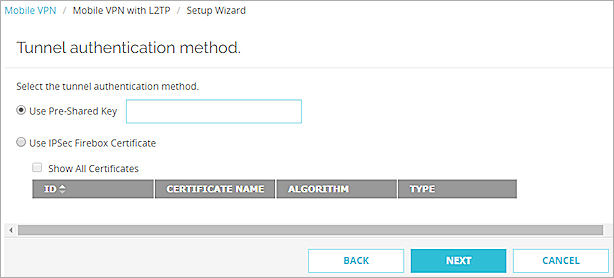
- Select an option for IPSec tunnel authentication. There are two options:
Use Pre-Shared Key
Type or paste the shared key. You must use the same pre-shared key in the IPSec settings on the L2TP client.
Use IPSec Firebox Certificate
Select the certificate to use from the table. You must have already imported a certificate to the Firebox to use this option.
To use certificates for authentication, you must install the certificate on all devices that connect.
For more information, go to Certificates for Mobile VPN with L2TP Tunnel Authentication.
- Click Next.
- Click Finish to save the configuration and exit the wizard.
- Select VPN > Mobile VPN > L2TP.
The WatchGuard L2TP Setup Wizard opens. - Click Next.
A list of configured authentication servers opens.
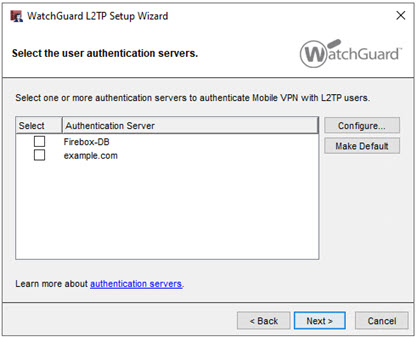
- Select the check box for each authentication server you want to use for Mobile VPN with L2TP user authentication. You can add the internal Firebox database (Firebox-DB) and one or more RADIUS servers.
For more information about user authentication methods for L2TP, go to About Mobile VPN with L2TP User Authentication - To specify a different default server, select the check box for that server and click Make Default.
If users do not specify the authentication server as part of the user name when they authentication from an L2TP client, Mobile VPN with L2TP uses the default authentication server.
If you select more than one authentication server, users who use the non-default authentication server must specify the authentication server or domain as part of the user name. For more information and examples, go to Connect from an L2TP VPN Client.
- After you have selected authentication servers, click Next.
The Add users and groups page opens. The L2TP-Users group is automatically added by default.
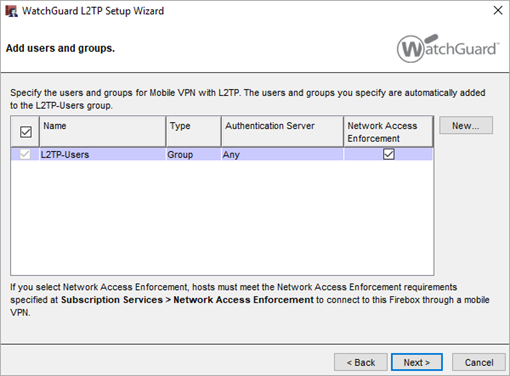
- Select the users or groups for Mobile VPN with L2TP.
- (Optional) To apply enforcement settings to Mobile VPN with L2TP groups:
- Select the check box for a group.
- In Fireware v12.9 or higher, select the Network Access Enforcement check box.
- To disable enforcement for a group, select the check box for that group and select No.
- To add new users or groups to authenticate with Mobile VPN with L2TP:
- Click New.
- Select Firebox-DB User/Group or External User/Group.
- If you selected Firebox-DB User/Group for the authentication server, follow the instructions in the Define a New User for Firebox Authentication or Define a New Group for Firebox Authentication topics to add a new user or group.
- If you selected External User/Group, configure the settings in the Add User or Group dialog box.
- (Optional) To apply enforcement settings to the group in Fireware v12.9 or higher, select Enable Network Access Enforcement. For more information, go to Network Access Enforcement Overview.
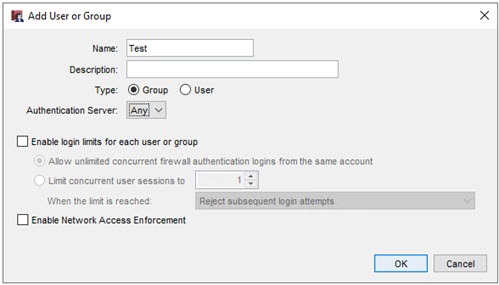
If you use the Firebox-DB for authentication you must use the L2TP-Users group that is created by default. You can add the names of other groups and users that use Mobile VPN with L2TP. For each group or user you add, you can select the authentication server where the group exists, or select Any if that group exists on more than one authentication server. The group or user name you add must exist on the authentication server. The group and user names are case sensitive and must exactly match the name on your authentication server.
- After you configure users and groups, click Next.
The Configure the allowed resources page opens.
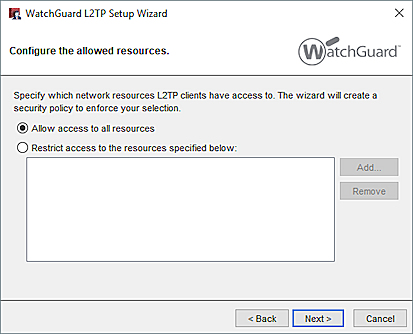
The allowed resources determine what the wizard puts in the To section of the automatically generated Allow L2TP-Users policy. Unless you restrict access to specific resources, the Allow L2TP-Users policy allows access to Any.
- To limit access, select Restrict access to the resources specified below.
- Click Add to add network IP address ranges, aliases, or other resources you want Mobile VPN with L2TP users to have access to.
- After you have configured the allowed resources, click Next.
The Virtual IP Address Pool page opens. By default, the 192.168.115.0/24 network shows in the list.
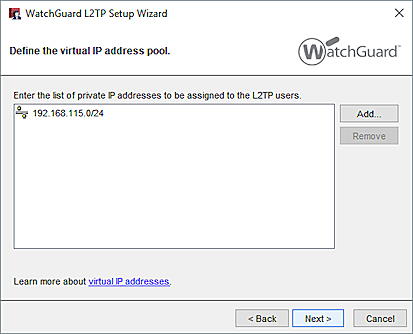
- Click Add to add an IPv4 host address, network address, or address range. You must add at least two IP addresses to the virtual IP address pool.
For more information about virtual IP address pools, go to Virtual IP Addresses and Mobile VPNs.
- After you define the virtual IP address pool, click Next.
The Select the tunnel authentication method page opens.
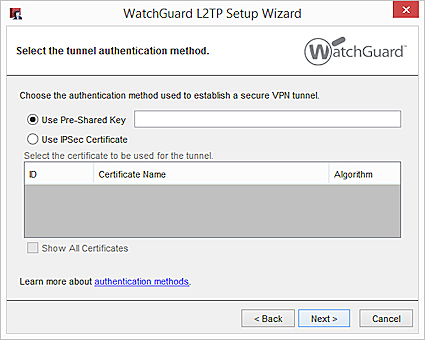
- Select an option for IPSec tunnel authentication. There are two options:
Use Pre-Shared Key
Type or paste the shared key. You must use the same pre-shared key in the IPSec settings on the L2TP client.
Use IPSec Certificate
Select the certificate to use from the table. You must have already imported a certificate to the Firebox to use this option.
For more information, go to Certificates for Mobile VPN with L2TP Tunnel Authentication.
- Click Next.
The L2TP wizard is complete. - If you want to edit the L2TP configuration after the wizard is finished, select the Open the L2TP configuration dialog check box.
- Click Finish to close the wizard.
Mobile VPN with L2TP is enabled and the required L2TP policies are automatically added.
To configure other settings, edit the Mobile VPN with L2TP configuration.
When you enable Mobile VPN with L2TP, two policies are automatically added to allow L2TP traffic. For more information, go to About L2TP Policies.