To enforce compliance of mobile devices that connect to on-premises applications, file servers, or any other network resource protected by your Firebox, you can use Mobile Security. Mobile Security enforcement applies only to traffic that is routed through the Firebox.
To fully protect resources on your network from Android and iOS devices that are not compliant we recommend that you:
- Do not bridge a wireless network to the trusted or optional network
- Do not configure Mobile VPN with SSL to bridge VPN traffic
- Do not connect an AP device to a switch behind the Firebox that connects to other network resources on the same logical network.
Mobile Security enforcement does not apply to:
- Traffic from a connected mobile device to any other resource on the same subnet
- Traffic from a connected mobile device to a resource accessible through a router behind the Firebox, if the traffic does not go through the Firebox
The examples below show how you can add Mobile Security to protect resources from mobile devices that connect to Firebox through a wireless or VPN connection.
Because mobile devices can use networks that are not connected to your Firebox to connect to resources outside your network (such as web servers or cloud-based applications), Mobile Security cannot enforce mobile device compliance for resources that are not inside your network.
Mobile Security for Wireless Connections
To use Mobile Security to protect your network resources from mobile devices that connect to a wireless network, make sure that wireless users connect to a separate network subnet. Some options for how to add Mobile Security to your wireless network are described in these examples.
For more information about how to configure these AP device deployment examples, go to WatchGuard AP Deployment Examples.
Example 1 — Wireless AP Device Connected Directly to a Firebox
In this example, the AP device is connected directly to the Trusted-2 Firebox interface. If you enable Mobile Security enforcement for the Trusted-2 interface, Mobile Security drops traffic received on that interface from mobile devices that are not compliant. This protects the wired LAN connected to Trusted-1 and any other network resources that can be accessed through the Firebox.
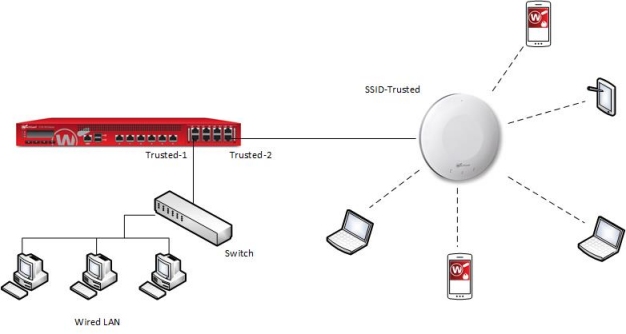
Because the traffic between the wireless clients that are connected to your AP device is not routed through the Firebox, Mobile Security does not apply to the traffic between the wireless clients. To prevent direct communication of wireless clients through the AP device, you can enable station isolation in the SSID settings on the AP device.
For more information about client isolation, go to About AP Client Isolation.
Example 2 — AP Device Connected to a Switch
In this example, the AP device is connected to a switch on the trusted network of the Firebox. If you enable Mobile Security enforcement for the interface the switch connects to (Trusted-2), Mobile Security drops all traffic received on the Trusted-2 interface from mobile devices that are not compliant. This means that Mobile Security protects the network resources on the Trusted-1 network, and on any other network resources that can be accessed by mobile devices through the Firebox.
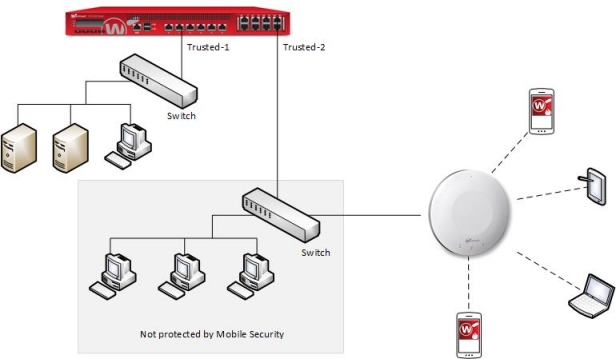
With this configuration, Mobile Security cannot protect the wired LAN that connects to the same switch as the AP device because the traffic from mobile devices to that network does not go through the Firebox. To enable Mobile Security enforcement for traffic from the wireless mobile devices to the network that connects to the same switch, you can use VLANs to logically separate the networks, as described in the next example.
Example 3 — AP Device Connected to a Switch with VLANs
In this example, the AP device is connected to a managed switch, and VLANs are used to separate the traffic through the SSIDs from each other, and from other parts of the network behind the Firebox. Multiple AP devices are connected to a managed switch. VLANs are configured for each SSID and for the wired network connected to the switch. Policies for VLAN10 (the VLAN assigned to the Trusted SSID) allow wireless clients to connect to resources on the wired LAN. Policies for the VLAN20 (the VLAN for the Guest SSID) do not allow guests to connect to internal network resources.
If you enable Mobile Security enforcement for the VLAN associated with the SSID that trusted wireless clients connect to, Mobile Security applies to all traffic from the mobile devices on that VLAN to any other VLAN or network connected to the Firebox. The wireless guest network does not need Mobile Security because the existing policies do not allow guest users to connect to internal network resources.
Unlike the previous example, Mobile Security does protect the wired LAN connected to the same switch. The wireless LAN is on a different logical network than the VLAN that trusted wireless users connect to.
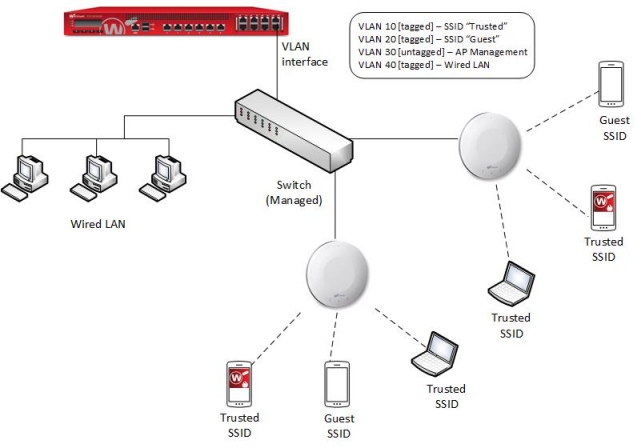
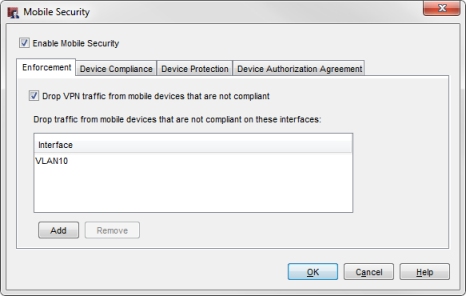
To enable Mobile Security enforcement for connections to the Trusted SSID, add VLAN10 to the Interface list in the Mobile Security Enforcement settings.
For more information about how to configure the VLANs and SSIDs as shown in this example, go to AP Deployment with VLANs and Guest Network.
If the VLAN used by the SSID for trusted users is bridged across more than one Firebox interface, you can enforce Firewall policies and Mobile Security settings for traffic that passes through the firewall between hosts on the same VLAN. To do this, in the VLAN configuration, select the Apply firewall policies to intra-VLAN traffic check box. For more information, go to Define a New VLAN.
Example 4 — Mobile Security on a Wireless Firebox
On a Firebox with built-in wireless, such as a T50-W or T30-W, you configure the wireless access point with the same type of settings as an internal network interface. To enable Mobile Security for a Firebox wireless access point, add the wireless interface to the Interface list in the Mobile Security configuration.
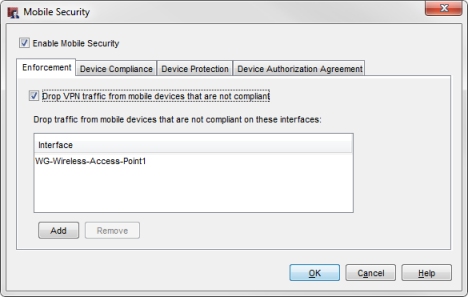
Mobile Security drops traffic that is not compliant for mobile devices that connect to the specified wireless network. This protects all other networks that can be accessed by the Firebox.
If the wireless interface is a member of a LAN bridge, the Firebox cannot enforce Mobile Security on connections from mobile devices to other network resources that are connected to the same bridged network.
Mobile Security does not apply to traffic between wireless clients that are connected to the same wireless access point because that traffic is on the same subnet. To prevent direct communication between wireless clients through the wireless network, in the Wireless Access Point configuration, you can select the Prohibit client to client wireless network traffic check box. For more information, go to Enable Wireless Connections.
Mobile Security for VPN Connections
In this example, a network has Fireboxes at several locations, all connected through BOVPN tunnels. Mobile VPN connections are allowed only to the Colocation Firebox. BOVPN tunnel switching is used to provide access to the networks protected by the other Fireboxes.
To enable Mobile Security enforcement for mobile devices that use a VPN client to connect to this network, you must enable Mobile Security on the Firebox that the Mobile VPN clients connect to. In this example, the Mobile VPN clients connect to the Colocation Firebox.
After Mobile Security confirms that a mobile device connected through a VPN is compliant, the Firebox allows traffic from that device to network resources based on the configured firewall policies. This includes traffic from the compliant mobile device to resources that can be accessed through a BOVPN tunnel.
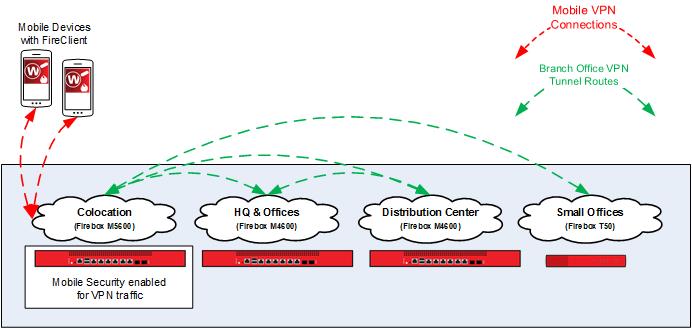
To enable Mobile Security for traffic from mobile devices that connect through a VPN, enable Mobile Security on the Firebox that mobile VPN clients connect to. In this example, when you enable Mobile Security on the Colocation Firebox, Mobile Security drops traffic from mobile devices that are not compliant before it can reach any of the other connected Fireboxes or networks.
To enable Mobile Security enforcement for VPN traffic, in the Mobile Security Enforcement settings, select the Drop VPN traffic from mobile devices that are not compliant check box. For more information, go to Configure Mobile Security Enforcement.
For information about how to configure BOVPN tunnel switching as shown in this diagram, see the Hybrid VPN configuration example on the Configuration Examples page.