In Fireware v12.9 or higher, you can use a RADIUS server to authenticate users to the WatchGuard Management Server. This enables you to use multi-factor and RADIUS challenge and response authentication with WatchGuard Management Server.
To support RADIUS and multi-factor authentication with the WatchGuard Management Server, you must use WatchGuard System Manager 12.9 or higher. Make sure the WatchGuard System Manager client and WatchGuard Management Server are the same version.
- Supports multi-factor authentication (MFA) services such as AuthPoint. For more information on how to integrate AuthPoint with the WatchGuard Management Server, go to WatchGuard Management Server Integration with AuthPoint.
- Supports password only (non-MFA), One-Time Password (OTP) when combined with a password, and push notifications.
- Supports RADIUS authentication servers for traditional password challenge and response authentication.
- The challenge from the RADIUS server appears to the user.
- The RADIUS server sends the one-time code to the user in an email or other delivery method.
- The user enters their code that is sent back to the RADIUS server.
- Supports multiple rounds of challenges and responses.
- Supports shared authentication sessions for Management Server, WatchGuard System Manager (WSM), Policy Manager, Firebox System Manager (FSM), and other applications (except for WebCenter). After you start an authenticated session with WatchGuard System Manager (WSM):
- Any new sessions you start from Firebox System Manager (FSM), Policy Manager, or other applications, share the same authentication session. A new authentication session is not started.
- Sessions are only shared from WatchGuard System Manager (WSM) as the parent application to the other applications. For example, if you authenticate a session in Policy Manager, it does not share the session with WSM or FSM.
- WebCenter is the exception and uses a separate authentication session.
RADIUS and Authentication Priority
WatchGuard System Manager will try to log in with this authentication priority:
- Local user
- Active Directory user (if Active Directory is enabled)
- RADIUS user (if RADIUS is enabled)
If you enable both Active Directory and RADIUS authentication, and both methods can authenticate with the same user name and password, then RADIUS authentication takes priority for multi-factor authentication.
Enable RADIUS Authentication on the Management Server
To use RADIUS to authenticate users, when you configure the settings for your Management Server you must define the connection information for the RADIUS server.
To enable and configure RADIUS authentication, from WatchGuard Server Center:
- In the Servers tree, select Management Server.
- Select the RADIUS tab.
The Management Server RADIUS page appears.
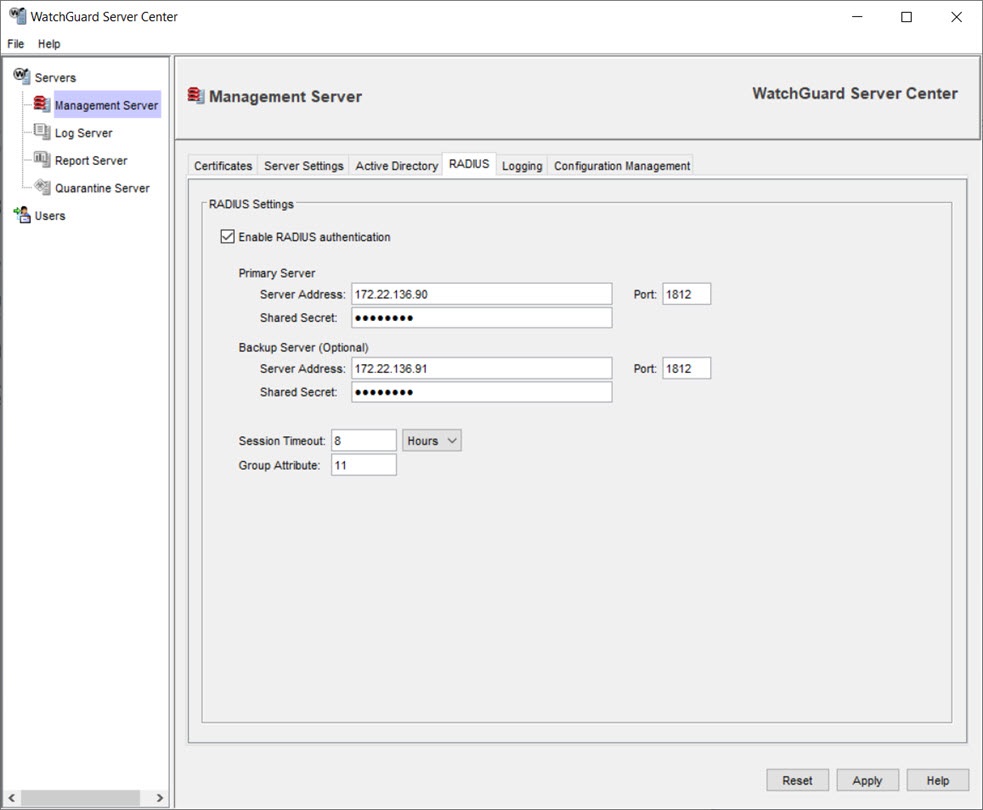
- Select the Enable RADIUS authentication check box.
- In the Primary Server Server Address text box, type the IP address or host name of the RADIUS server.
- In the Port text box, type the port number of the RADIUS server. The default is 1812.
- In the Shared Secret text box, type the shared secret for the RADIUS server. This must match the shared secret configured on the RADIUS server.
- Configure these settings for an optional Backup Server to use when the primary RADIUS server you configured is unavailable.
- In the Group Attribute text box, type a value for the group attribute on the RADIUS server for group authentication. The default is 11.
- In the Session Timeout text box, type a value for the session timeout that determines how long the authenticated session with the RADIUS server is valid. The default is 8 hours.
- Click Apply to save your configuration changes.
To configure users or groups to use with RADIUS authentication, go to Define or Remove Users or Groups.
Define or Remove Users or Groups