If you have two or more remote Branch Office VPN (BOVPN) tunnels connected to your network, and you want computers on the remote networks to exchange data, you must configure tunnel switching on the central Firebox. When you set up tunnel switching, the central Firebox decrypts packets sent from one VPN, applies the policies configured on the central Firebox, encrypts the packets again, and sends the encrypted packets to their destination on the other VPN.
For example, if you have a Firebox at your Central Office that you use for tunnel switching between BOVPN tunnels to two remote offices, your network configuration might look like this:
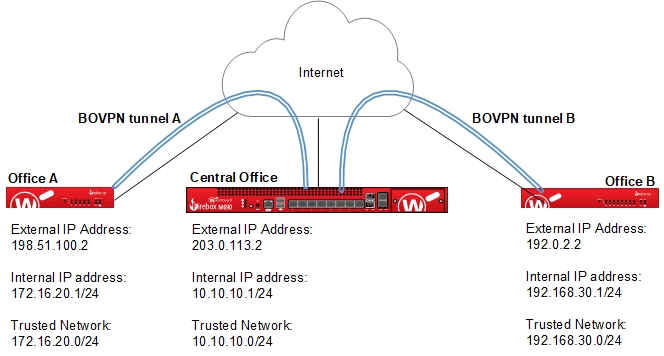
In this example, you can use tunnel switching so the Central Office Firebox can pass traffic from the trusted network of Remote Office A to the trusted network of Remote Office B, without a third BOVPN tunnel between the two remote offices. This configuration is useful when you require control of network security at the Central Office, because you can apply policies to traffic between the two tunnels at the Central Office.
For a step-by-step example of how to configure BOVPN tunnel switching in Policy Manager, go to Configure Manual Branch Office VPN Tunnel Switching.
When you link multiple sites together with branch office VPN tunnels, there are several different VPN topologies you could use:
- Centralized (Hub and Spoke)
- Decentralized (Full Mesh)
- Hybrid (Partial Mesh)
Go to the Configuration Examples page for example configuration files for each VPN topology and a description of each configuration.