Virtual Interface IP Addresses for a VPN to a Third-Party Endpoint
Third-party gateway that supports GRE over IPSec
You can configure a BOVPN virtual interface between your Firebox and a third-party VPN endpoint that supports GRE over IPSec. The third-party endpoint must terminate the GRE tunnel, not pass the GRE traffic through the IPSec tunnel.
To configure this type of BOVPN virtual interface, set the Remote Endpoint Type to Firebox.
Cloud VPN or third-party gateway without GRE
You can configure a BOVPN virtual interface between your Firebox and a Cloud VPN or third-party VPN gateway that does not use GRE. Fireware supports connections to cloud-based endpoints that support wildcard traffic selectors, for example, Microsoft Azure.
To configure this type of BOVPN virtual interface, set the Remote Endpoint Type to Cloud or Third-Party Gateway.
You configure virtual interface IP addresses the same way for either type of BOVPN virtual interface.
In Fireware v12.4 or higher, if you specify IPv6 Addresses as the Gateway Address Family, you must specify IPv6 virtual interface IP addresses.
Static Routing
To create static BOVPN virtual interface routes between a Firebox and a third-party device:
- Select the Firebox endpoint type to create an IPSec tunnel that uses GRE.
- Select Cloud or Third-Party Endpoint to create an IPSec tunnel without GRE.
For configuration examples, go to BOVPN Virtual Interface for Static Routing to Microsoft Azure, BOVPN Virtual Interface for Static Routing to Amazon Web Services (AWS), and Fireware Integration Guides.
Dynamic Routing
To use the BOVPN virtual interface for dynamic routing to a third-party VPN endpoint, you must configure the virtual interface IP address differently than for dynamic routing between two Fireboxes. For configuration examples, go to:
- BOVPN Virtual Interface for Dynamic Routing to Cisco
- BOVPN Virtual Interface for Dynamic Routing to Microsoft Azure
- BOVPN Virtual Interface for Dynamic Routing to Amazon Web Services (AWS)
For a BOVPN virtual interface to a third-party device, you specify a local IP address and a subnet mask:
- Local IP address — The IP address to use for the local end of the tunnel. It must be on the same subnet as the local IP address configured for this VPN on the third-party VPN endpoint.
- Peer IP address or netmask — The subnet mask for the local IP address. It must be the same as the netmask configured for this VPN on the third-party endpoint. For dynamic routing to a Microsoft Azure network, specify the Azure virtual interface IP address instead of a netmask. The Azure virtual interface IP address is defined by Azure.
To make sure that the addresses you specify do not conflict with any other devices, we recommend that you select a local IP address and netmask in a private network IP address range that is not used by any local network or by any remote network connected through a VPN.
If you enable a BOVPN virtual interface for a FireCluster, make sure that the Local IP address does not conflict with the cluster interface IP addresses or the cluster management IP addresses. The WatchGuard BOVPN virtual interface supports BGP and OSPF. However, dynamic routing with OSPF to Microsoft Azure and Amazon AWS is not currently supported.
Maximum Transmission Unit (MTU)
In Fireware v12.5 or higher, you can specify a custom maximum transmission unit (MTU) value for BOVPN virtual interfaces. You might need to do this if your Firebox connects to a third-party VPN endpoint that requires a custom MTU value. For example, a Microsoft Azure VPN gateway requires an MTU of 1400. To determine whether the third-party endpoint requires a custom MTU value, see the documentation provided by the third-party vendor.
For more information about the MTU setting, go to About BOVPN Virtual Interfaces.
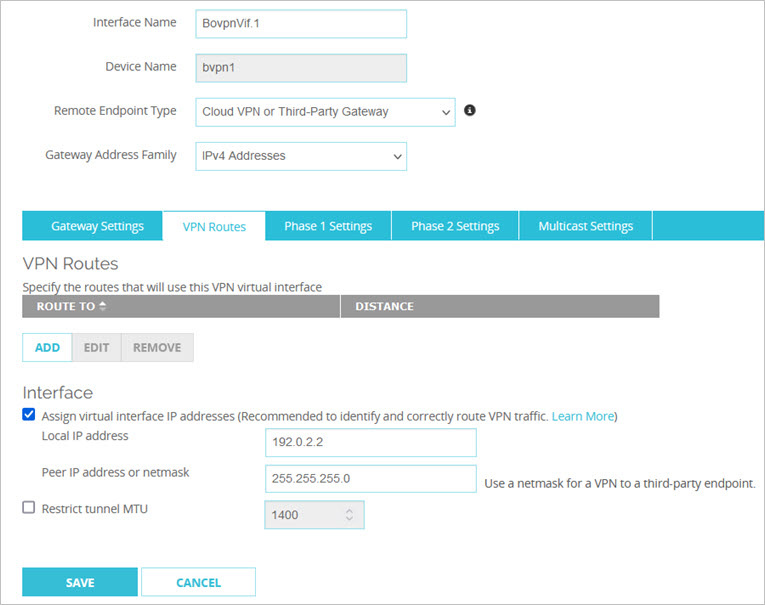
Assign Virtual IP Addresses
- Add or edit a BOVPN virtual interface.
For more information, go to Configure a BOVPN Virtual Interface. - Select the VPN Routes tab.
- In the Interface section, select the Assign virtual interface IP addresses check box.
- In the Local IP address text box, type the IP address for the local end of the tunnel. This address must be on the same subnet as the IP address configured for this VPN tunnel on the third-party endpoint (the peer).
- In the Peer IP address or netmask text box, type the netmask.
The netmask must be the same as the netmask configured for this VPN tunnel on the third-party endpoint.
- Add or edit a BOVPN virtual interface.
For more information, go to Configure a BOVPN Virtual Interface. - Select the VPN Routes tab.
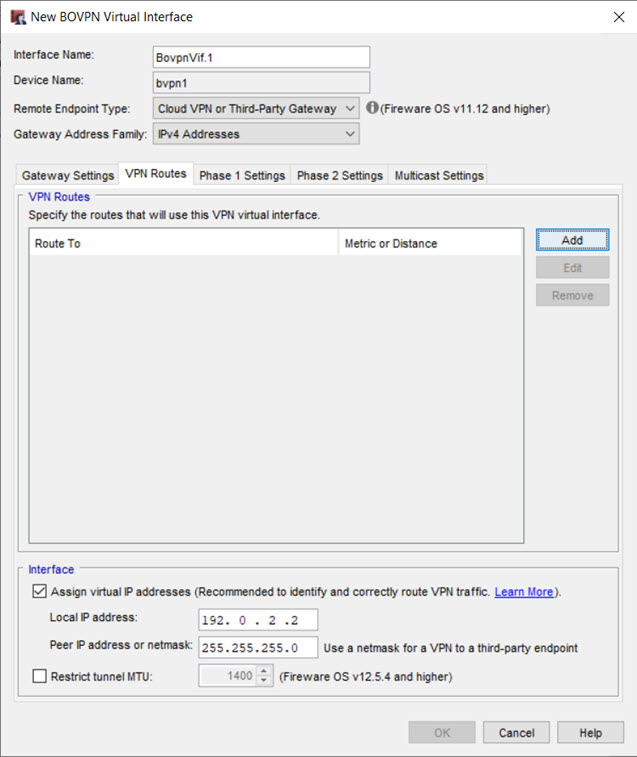
- In the Interface section, select the Assign virtual interface IP addresses check box.
- In the Local IP address text box, type the IP address for the local end of the tunnel.
This address must be on the same subnet as the IP address configured for this VPN tunnel on the third-party endpoint (the peer). - In the Peer IP address or netmask text box, type the netmask.
The netmask must be the same as the netmask configured for this VPN tunnel on the third-party endpoint.
When you configure dynamic routing through the BOVPN virtual interface, use the virtual interface network IP address, not the device name in the dynamic routing configuration. For example, if the BOVPN virtual interface local IP address is 10.10.11.0 and the netmask is 255.255.255.0, specify the 10.10.11.0/24 address in the dynamic routing configuration.