BOVPN over TLS uses a client-server model for VPN tunnel communication. You must configure at least one Firebox as a BOVPN over TLS Client and at least one Firebox as a BOVPN over TLS Server.
In Fireware v12.1, you must use the Web UI to configure BOVPN over TLS. In Fireware v12.1.1 and higher, you can also use Policy Manager.
About SSL/TLS Settings Precedence and Inheritance
Several Firebox features use SSL/TLS for secure communication. In order of precedence from highest to lowest, those features are:
- Management Tunnel over SSL on hub devices
- BOVPN over TLS in Server mode
- Mobile VPN with SSL
- Access Portal
Features with lower precedence inherit some SSL/TLS settings from enabled features with higher precedence. The shared settings are not configurable for the features with lower precedence.
If Management Tunnel over SSL is enabled, these BOVPN over TLS settings are not configurable:
- Primary Server
- Backup Server
- Advanced settings — Virtual IP address pool, Authentication, Encryption, Data Channel, Keep-Alive Interval, Keep-Alive Timeout, Renegotiate Data Channel
BOVPN over TLS Server mode settings take precedence over some settings for Mobile VPN with SSL and the Access Portal. For information about how BOVPN over TLS Server mode settings affect Mobile VPN with SSL and Access Portal settings, go to SSL/TLS Settings Precedence and Inheritance.
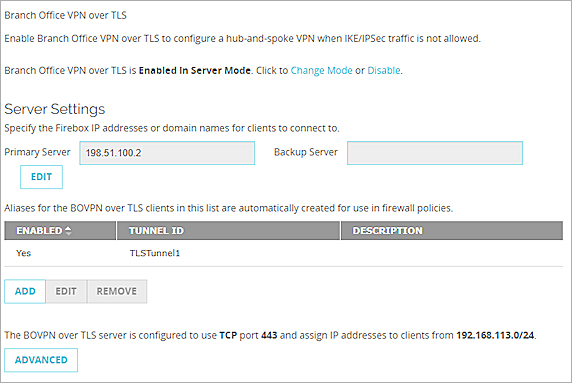
Enable Server Mode
When you enable BOVPN over TLS in Server mode, your Firebox is configured as a TLS server.
- Select VPN > BOVPN over TLS.
- Click Enable.
The BOVPN over TLS Mode dialog box appears. - From the Firebox Mode drop-down list, select Server.
- In the Primary Server text box, type a Firebox IP address or domain name for client connections.
- (Optional) In the Backup Server text box, type the IP address or domain name for a secondary external interface on the Firebox. The client tries to connect to the backup server if it cannot connect to the primary server.
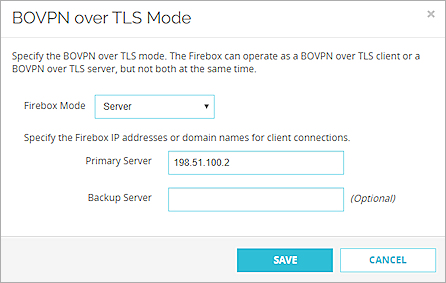
- Click Save.
A summary of the configuration appears.
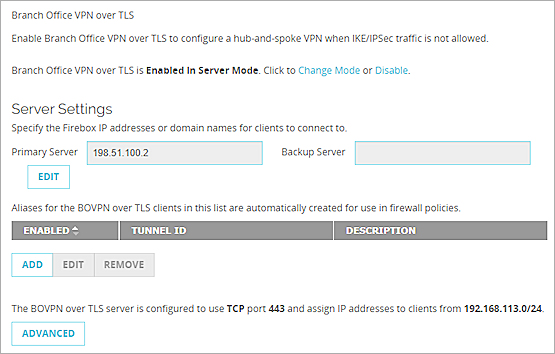
Next, you must add a BOVPN over TLS client that can connect to the BOVPN over TLS server.
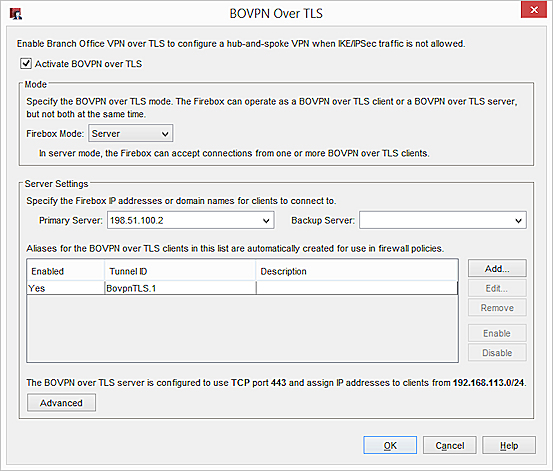
- Select VPN > BOVPN over TLS.
- Select Activate BOVPN over TLS.
- From the Firebox Mode drop-down list, select Server.
- In the Primary Server text box, type a Firebox IP address or domain name for client connections.
- (Optional) In the Backup Server text box, type the IP address or domain name for a secondary external interface on the Firebox. The client tries to connect to the backup server if it cannot connect to the primary server.
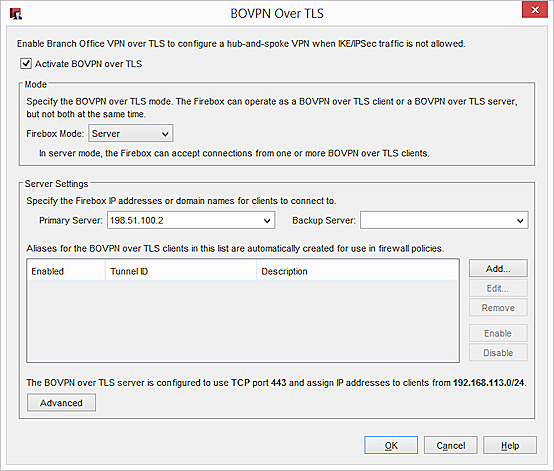
Next, you must add a BOVPN over TLS client that can connect to the BOVPN over TLS server.
Add a BOVPN over TLS Client
When you add a BOVPN over TLS Client, you must specify:
- Client Routes — Destinations behind the BOVPN over TLS server that are accessible by the BOVPN over TLS client. Select to send all traffic through the tunnel or only traffic to destinations that you specify.
- Server Routes — Destinations behind the BOVPN over TLS client that are accessible by the BOVPN over TLS server.
If Mobile VPN with SSL is enabled on the BOVPN over TLS Client, you must select the Specify the destination addresses that the client will route through the tunnel option on the BOVPN over TLS Server. If you select Traffic destined for all locations is sent through the tunnel, mobile users cannot make a Mobile VPN with SSL connection to the Firebox configured as a BOVPN over TLS Client.
- Click Add.
The Add Client page appears.
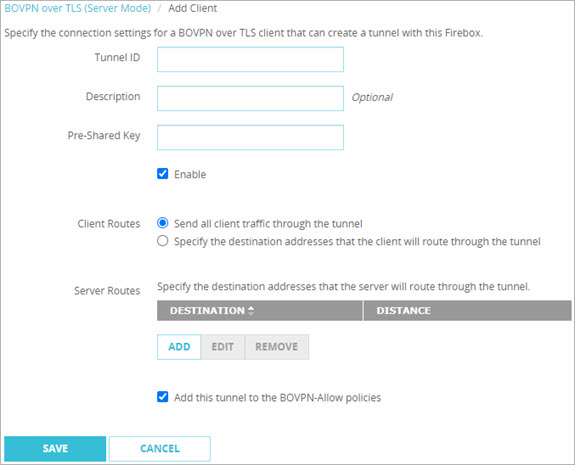
- In the Tunnel ID text box, type a name to identify the tunnel. You must specify the same Tunnel ID on the TLS client.
- (Optional) In the Description text box, type a description of the tunnel.
- In Pre-Shared Key text box, type the pre-shared key that the client and server use.
- To enable this client, select Enable.
- In the Client Routes section, specify what traffic the BOVPN over TLS client sends through the tunnel.
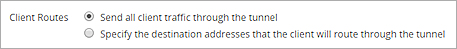
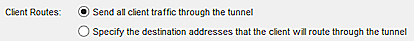
Send all client traffic through the tunnel
Traffic destined for all locations is sent through the tunnel.
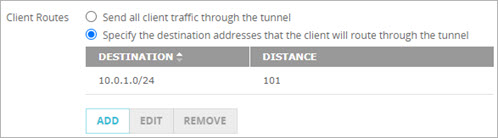
Specify the destination addresses that the client will route through the tunnel.
Only traffic destined for the specified network or host IP addresses behind the BOVPN over TLS Server is sent through the tunnel.
- In the Server Routes section, click Add.
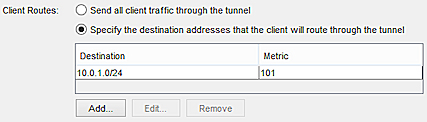
The Route dialog box appears. - In the Destination Type drop-down list, select Network IPv4 or Host IPv4.
- In the Route To text boxes, type the network or host IP address.
- In the Distance text box, type the metric for the route. In Fireware v12.9 or higher, the Distance setting replaces the Metric setting.
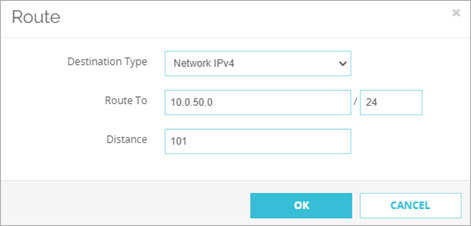
- Click OK to view the tunnel configuration.
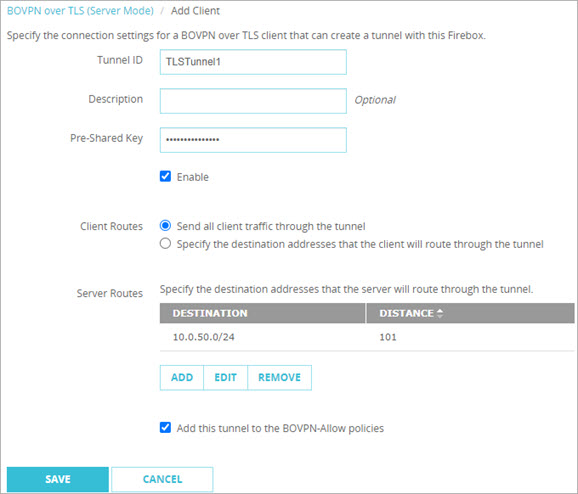
The Send all client traffic through tunnel option in the Web UI
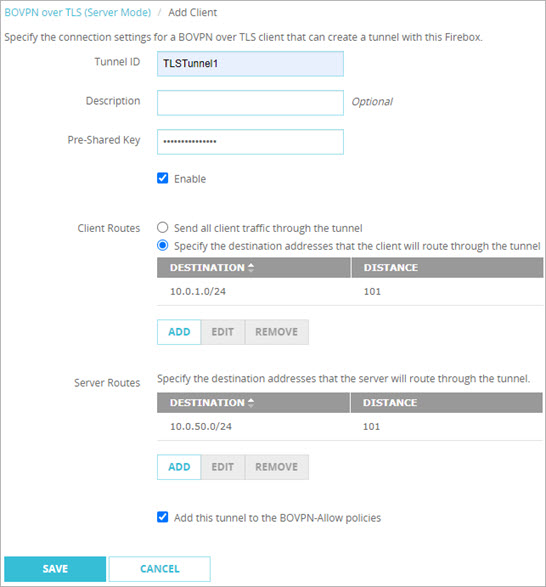
The Specify the destination addresses that the client will route through the tunnel option in the Web UI
- Click Save.
A summary of the configuration appears.
- Click Add.
The Add Client dialog box appears.
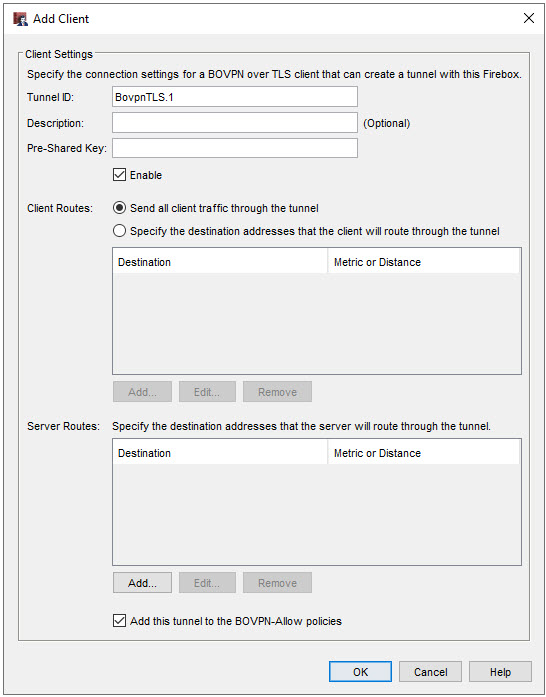
- In the Tunnel ID text box, type a name to identify the tunnel. You must specify the same Tunnel ID on the TLS client.
- (Optional) In the Description text box, type a description of the tunnel.
- In Pre-Shared Key text box, type the pre-shared key that the client and server use.
- To enable this client, select Enable.
- In the Client Routes section, specify what traffic the BOVPN over TLS client sends through the tunnel.
Send all client traffic through the tunnel
Traffic destined for all locations is sent through the tunnel.
Specify the destination addresses that the client will route through the tunnel
Only traffic destined for the specified network or host IP addresses behind the BOVPN over TLS Server is sent through the tunnel
- In the Server Routes section, click Add.
The Add Route dialog box appears. - From the Destination Type drop-down list, select Network IPv4 or Host IPv4.
- In the Route To text box, type the network or host IP address.
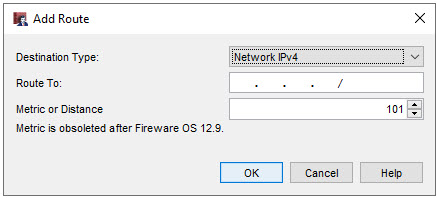
- In the Metric or Distance text box, type the distance for the route. In Fireware v12.9 or higher, the Distance setting replaces the Metric setting.
- Click OK to view the tunnel configuration.
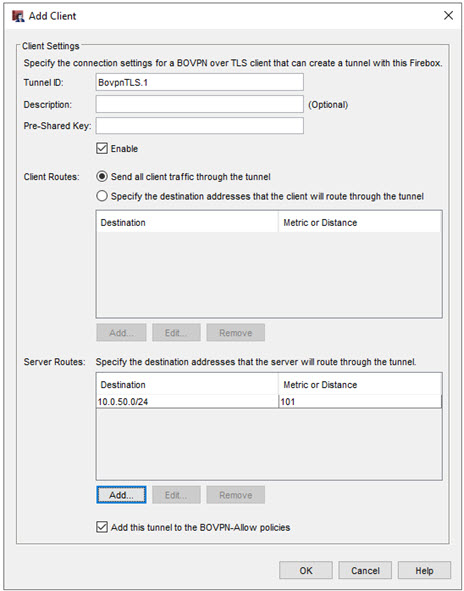
The Send all client traffic through tunnel option in Policy Manager
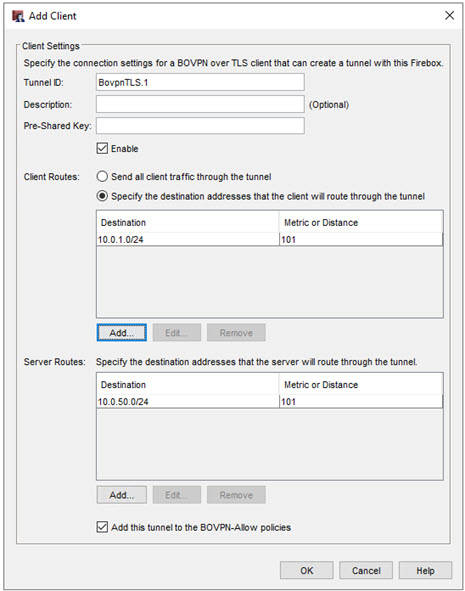
The Specify the destination addresses that the client will route through the tunnel option in Policy Manager
- Click OK.
A summary of the configuration appears.
Configure Advanced Settings
The Advanced Settings include these communication settings.
IP Address Pool
By default, the BOVPN over TLS server assigns addresses in the 192.168.113.0/24 pool to BOVPN over TLS clients. Mobile VPN with SSL also uses the 192.168.113.0/24 pool by default. If BOVPN over TLS in Client mode and Mobile VPN with SSL are both enabled on the same Firebox, you must specify a different IP address pool for one of these features. If both features use the same IP address pool, BOVPN over TLS traffic is not sent through the tunnel correctly.
You cannot configure the IP Address Pool setting if Management Tunnel over SSL is enabled.
Authentication
Select an authentication method for the connection: SHA-1, SHA-256, or SHA-512. We recommend the SHA-2 variants, SHA-256 and SHA-512, that are stronger than SHA-1.
Encryption
Select an algorithm to encrypt the traffic: 3DES, AES (128-bit), AES (192-bit), or AES (256-bit). In Fireware v12.2 or higher, you can also select AES-GCM (128-bit), AES-GCM (192-bit), or AES-GCM (256-bit). We recommend AES encryption. For the best performance, choose a 128-bit AES variant. For the strongest encryption, choose a 256-bit AES variant.
If you select 3DES, be aware of a potential, but unlikely, security attack. For more information, go to Sweet32 Vulnerability in the WatchGuard Knowledge Base.
Data Channel
If the data channel protocol is TCP, you cannot specify a port number other than 443.
You can change the data channel protocol to UDP and specify a different port unless Management Tunnel over SSL is enabled on your Management Server.
For information about the differences between TCP and UDP, go to Choose the Port and Protocol for Mobile VPN with SSL.
For information about settings precedence, go to SSL/TLS Settings Precedence and Inheritance.
Keep-Alive Interval
If no packets have been sent over the tunnel for the amount of time you specify, the BOVPN over TLS server pings the BOVPN over TLS client.
Keep-Alive Timeout
If the BOVPN over TLS client does not send a response or other packet before the Keep-Alive Timeout value elapses, the tunnel connection closes and restarts.
The Keep-Alive Timeout value is automatically doubled. For example, if you keep the default value of 60 seconds, the BOVPN over TLS server waits 120 seconds to receive packets from the BOVPN over TLS client. If 120 seconds elapse with no response from the BOVPN over TLS client, the tunnel connection closes and restarts. This makes sure the BOVPN over TLS client detects a timeout before the BOVPN over TLS server closes the connection.
Renegotiate Data Channel
If a BOVPN over TLS connection has been active for the amount of time specified in the Renegotiate Data Channel text box, the BOVPN over TLS server creates a new tunnel. The minimum value is 1 hour.
You cannot configure the Renegotiate Data Channel setting if Management Tunnel over SSL is enabled.
- On the BOVPN over TLS Server Settings page, click Advanced.
The Advanced Settings dialog box appears.
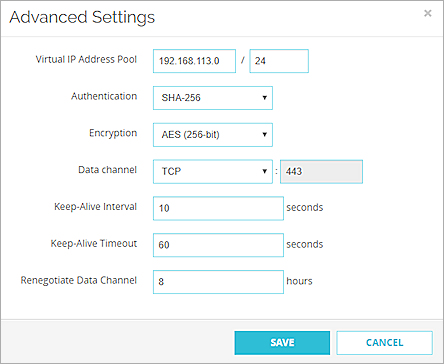
- In the Virtual IP Address Pool text box, type the network IP address.
- In the Authentication drop-down list, select SHA-1, SHA-256, or SHA-512.
- In the Encryption drop-down list, select 3DES, AES (128-bit), AES (192-bit), or AES (256-bit). In Fireware v12.2 or higher, you can also select AES-GCM (128-bit), AES-GCM (192-bit), or AES-GCM (256-bit).
- In the Data channel drop-down list, select TCP or UDP.
- If you selected UDP, specify a port number in the adjacent text box.
- In the Keep-Alive Interval text box, specify a number in seconds.
- In the Keep-Alive Timeout text box, specify a number in seconds.
- In the Renegotiate Data Channel text box, specify a number in hours.
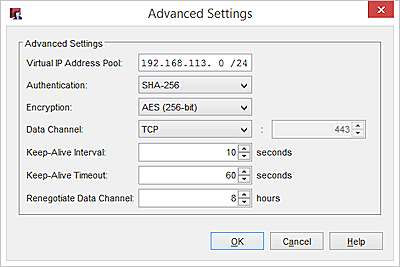
- On the BOVPN over TLS Server Settings dialog box, click Advanced.
The Advanced Settings dialog box appears - In the Virtual IP Address Pool text box, type the network IP address.
- In the Authentication drop-down list, select SHA-1, SHA-256, or SHA-512.
- In the Encryption drop-down list, select 3DES, AES (128-bit), AES (192-bit), or AES (256-bit). In Fireware v12.2 or higher, you can also select AES-GCM (128-bit), AES-GCM (192-bit), or AES-GCM (256-bit).
- In the Data channel drop-down list, select TCP or UDP.
- If you selected UDP, specify a port number in the adjacent text box.
- In the Keep-Alive Interval text box, specify a number in seconds.
- In the Keep-Alive Timeout text box, specify a number in seconds.
- In the Renegotiate Data Channel text box, specify a number in hours.
Configure BOVPN over TLS in Client Mode